Exploit
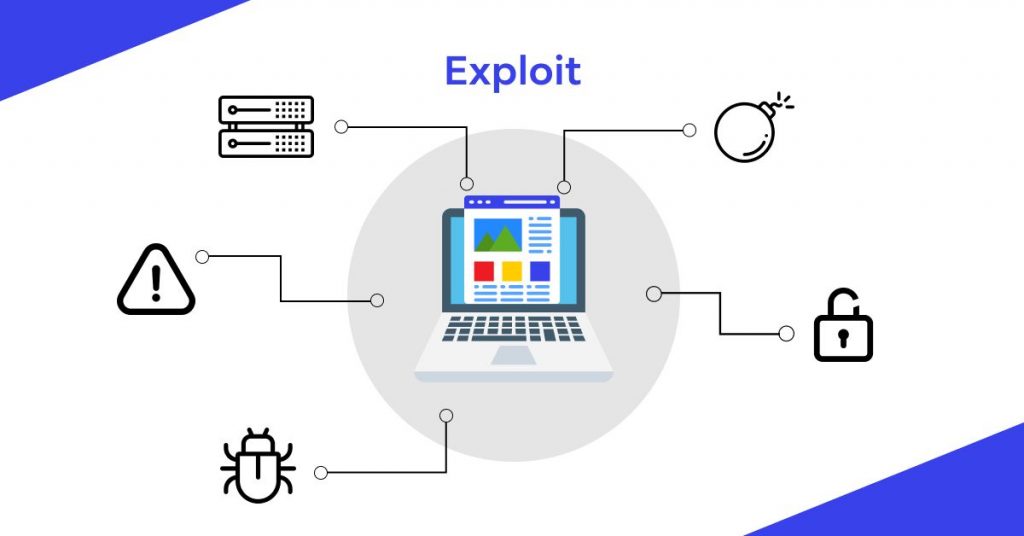
What is Exploit?
An exploit is a program or piece of code that is meant to detect and exploit a security fault or vulnerability in an application or computer system, generally for nefarious reasons such as malware installation. An exploit is a method used by cybercriminals to deliver malware rather than malware itself.
Understanding Exploit
Exploits comprise data or executable code that can exploit one or more software flaws on a local or remote computer. For example, suppose you have a browser with a vulnerability that allows the execution of “arbitrary code,” that is, the installation and execution of a malicious application on your system without your knowledge, or the induction of unexpected system behavior. Typically, attackers’ initial step is privilege escalation, which allows them to do whatever they want on the attacked system.
Browsers, along with Flash, Java, and Microsoft Office, are among the most targeted software categories. Because of their pervasiveness, they are actively examined by both security professionals and hackers, and browser developers are compelled to produce fixes to address vulnerabilities on a regular basis. It is advisable to install these fixes as soon as possible, but this is not always possible – after all, you will have to dismiss all tabs. Of course, exploitation of undiscovered vulnerabilities discovered and deployed by criminals, known as zero-day vulnerabilities, provide a unique challenge. It can take a long time for manufacturers to recognize and correct a problem.
Read related articles:
« Back to Glossary IndexDisclaimer
In line with the Trust Project guidelines, please note that the information provided on this page is not intended to be and should not be interpreted as legal, tax, investment, financial, or any other form of advice. It is important to only invest what you can afford to lose and to seek independent financial advice if you have any doubts. For further information, we suggest referring to the terms and conditions as well as the help and support pages provided by the issuer or advertiser. MetaversePost is committed to accurate, unbiased reporting, but market conditions are subject to change without notice.
About The Author
Damir is the team leader, product manager, and editor at Metaverse Post, covering topics such as AI/ML, AGI, LLMs, Metaverse, and Web3-related fields. His articles attract a massive audience of over a million users every month. He appears to be an expert with 10 years of experience in SEO and digital marketing. Damir has been mentioned in Mashable, Wired, Cointelegraph, The New Yorker, Inside.com, Entrepreneur, BeInCrypto, and other publications. He travels between the UAE, Turkey, Russia, and the CIS as a digital nomad. Damir earned a bachelor's degree in physics, which he believes has given him the critical thinking skills needed to be successful in the ever-changing landscape of the internet.
More articles
Damir is the team leader, product manager, and editor at Metaverse Post, covering topics such as AI/ML, AGI, LLMs, Metaverse, and Web3-related fields. His articles attract a massive audience of over a million users every month. He appears to be an expert with 10 years of experience in SEO and digital marketing. Damir has been mentioned in Mashable, Wired, Cointelegraph, The New Yorker, Inside.com, Entrepreneur, BeInCrypto, and other publications. He travels between the UAE, Turkey, Russia, and the CIS as a digital nomad. Damir earned a bachelor's degree in physics, which he believes has given him the critical thinking skills needed to be successful in the ever-changing landscape of the internet.


















































