Microsoft warns of “cryware” attacks that clear out crypto wallets

Microsoft has released a comprehensive study of so-called cryware, attacks that can attack crypto hot wallets in an effort to, well, steal your apes.
“Cryware are information stealers that collect and exfiltrate data directly from non-custodial cryptocurrency wallets, also known as hot wallets. Because hot wallets, unlike custodial wallets, are stored locally on a device and provide easier access to cryptographic keys needed to perform transactions, more and more threats are targeting them,” writes the Microsoft 365 Defender Research Team.
The researchers saw multiple types of attacks including ransomware attacks that locked users hot wallets until a ransom was paid. The cryware also looks for data that could indicate that the user has a crypto wallet on their computer and then attacks it, looking for keys and seed phrases.
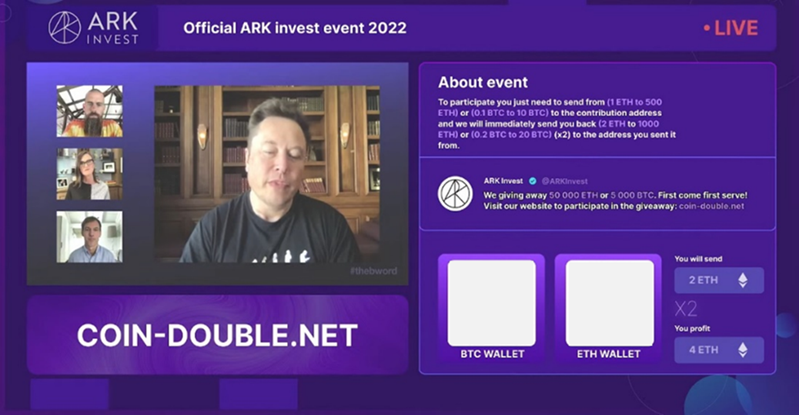
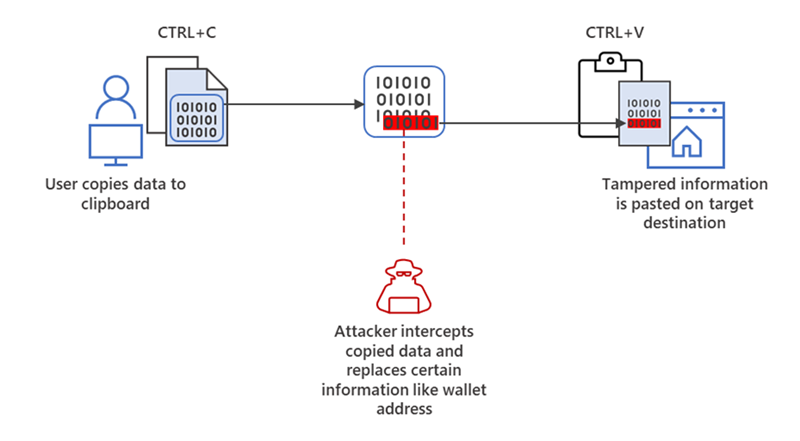
“To find hot wallet data such as private keys, seed phrases, and wallet addresses, attackers could use regular expressions (regexes), given how these typically follow a pattern of words or characters. These patterns are then implemented in cryware, thus automating the process. The attack types and techniques that attempt to steal these wallet data include clipping and switching, memory dumping, phishing, and scams,” the team wrote.
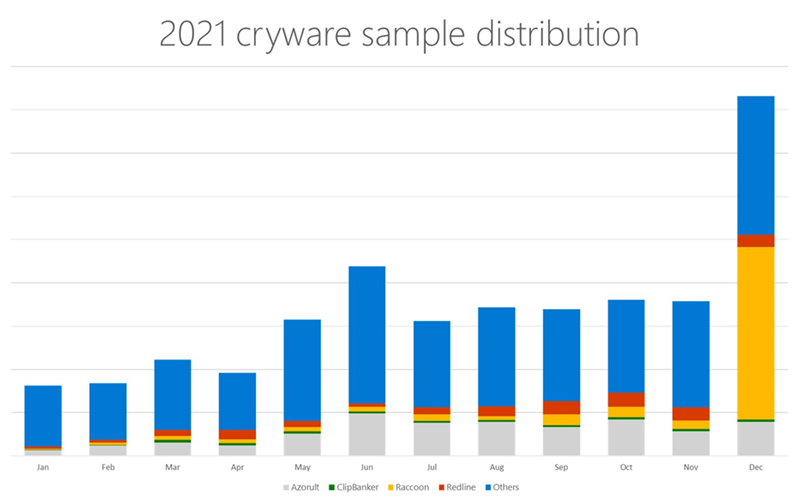
Cryware attacks have risen in the past year, hitting a high point last December. Microsoft recommends using antivirus software and being very careful when cutting and pasting wallet addresses. They have found a number of viruses that will “clip and switch,” a process that changes wallet addresses as they’re pasted into a text field.
Other cryware looks for seed phrases on your machine.
“For example, in 2021, a user posted about how they lost USD78,000 worth of Ethereum because they stored their wallet seed phrase in an insecure location. An attacker likely gained access to the target’s device and installed cryware that discovered the sensitive data. Once this data was compromised, the attacker would’ve been able to empty the targeted wallet,” wrote the researchers.
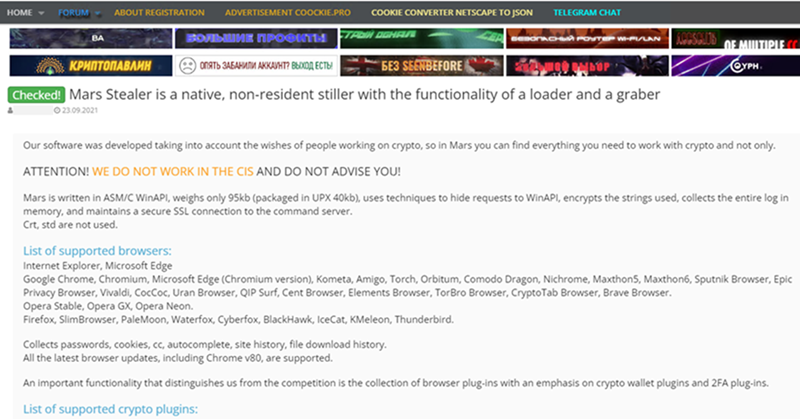
The report goes on to describe other attack vectors including Mars Stealer, a file exfiltration system that will steal wallet files and upload them to a central server. Their advice? Click carefully, be diligent when moving your crypto, and never believe scammers when they tell you you’ll get rich quick.
Read related posts:
- As crypto craters, scammers go after wallet keys
- Holoportation: How VR tech straight out of sci-fi will change the future of work
- Elon Musk gives slurp juice to the apes
Disclaimer
In line with the Trust Project guidelines, please note that the information provided on this page is not intended to be and should not be interpreted as legal, tax, investment, financial, or any other form of advice. It is important to only invest what you can afford to lose and to seek independent financial advice if you have any doubts. For further information, we suggest referring to the terms and conditions as well as the help and support pages provided by the issuer or advertiser. MetaversePost is committed to accurate, unbiased reporting, but market conditions are subject to change without notice.
About The Author
John Biggs is an entrepreneur, consultant, writer, and maker. He spent fifteen years as an editor for Gizmodo, CrunchGear, and TechCrunch and has a deep background in hardware startups, 3D printing, and blockchain. His work has appeared in Men’s Health, Wired, and the New York Times. He has written eight books including the best book on blogging, Bloggers Boot Camp, and a book about the most expensive timepiece ever made, Marie Antoinette’s Watch. He lives in Brooklyn, New York.
More articles

John Biggs is an entrepreneur, consultant, writer, and maker. He spent fifteen years as an editor for Gizmodo, CrunchGear, and TechCrunch and has a deep background in hardware startups, 3D printing, and blockchain. His work has appeared in Men’s Health, Wired, and the New York Times. He has written eight books including the best book on blogging, Bloggers Boot Camp, and a book about the most expensive timepiece ever made, Marie Antoinette’s Watch. He lives in Brooklyn, New York.


















































