Crypto Theft: How Cryptocurrency is Stolen and the Role of Law Enforcement in Asset Recovery

In Brief
Crypto theft is rising through scams, hacks, and fraud, but rapid response, blockchain forensics, and law enforcement collaboration are key to recovering stolen assets.

As the crypto market keeps expanding, so does the shadow that follows it — fraud, hacks, and phishing attacks are no longer edge cases. They’ve become part of the daily rhythm.
Blockchains promise transparency, sure — but when money gets stolen, the decentralized nature of crypto becomes its biggest drawback. No support desk. No refunds. No one to call. Victims often end up on their own, stuck in a system that even law enforcement is still learning to navigate.
In this piece, we’ll explore the main ways crypto theft happens today, the obstacles to recovering stolen funds, and how specialized teams are helping law enforcement tip the balance back toward the good guys.
Common Cryptocurrency Fraud Schemes in 2024-2025
Drainers – Wallet Exploitation Scams
Drainers aren’t brute-force tools. They’re quiet thieves — built to make users unlock the vault themselves.
The tactic is nearly always the same: get someone to visit a fake site, connect their wallet, and approve a transaction they don’t fully understand. That one signature? It’s all the attacker needs. Some versions go further — hiding malicious code inside fake browser extensions or posing as “helpful” wallet apps. Open it once, and your keys are already gone.
Case Study: Angel Drainer + Image
One of the most aggressive kits to surface in 2024 was Angel Drainer — used in attacks that drained over $25 million from more than 35,000 wallets.
A forensic investigation led by Match Systems tracked the operation through off-chain breadcrumbs: reused servers, overlapping browser fingerprints, and infrastructure patterns that eventually gave away the team behind it. The result? A rare win in the fight against wallet drainers — full exposure and shutdown.
Address Poisoning — Manipulating Transactions
Sometimes, it takes just one wrong click.
Address poisoning is a low-tech, high-impact scam where attackers slip a fake wallet address into your transaction history — hoping you’ll copy it by mistake.
They send a tiny amount of crypto from an address that looks almost identical to one you trust. That clone shows up in your recent transactions, and when you rush to send funds later… boom. You paste the wrong address — and the money’s gone. It’s one of the cheapest scams to run — and one of the hardest to reverse.
Case Study: $68M Recovery from Address Poisoning
In 2024, Match Systems tracked down a hacker who used this exact trick to steal $68 million.
The attacker stayed off KYC exchanges and tried to cover their tracks — but analysts dug deeper. They pulled IP logs, matched device fingerprints, and studied movement patterns across wallets. The end result? A full recovery — and a loud message to scammers: blockchain forensics is watching.
Exchange and Platform Hacks
Exchanges are where the big money lives — and hackers know it.
Billions in user deposits spread across hot and cold wallets, all behind a few layers of code and credentials. Sometimes, one weak spot is all it takes. Most breaches follow familiar patterns: phishing, stolen admin access, and overlooked security holes. But when they hit, they hit hard — and the losses are massive.
Here’s a look at some of the largest exchange hacks from 2024 and 2025 — each one a reminder that even the biggest platforms aren’t immune.
Case Study: Bybit Hack — February 2025
One of the biggest crypto heists on record. Attackers got into Bybit’s cold wallets and made off with around $1.5 billion, including over 400,000 ETH.
Investigators linked the operation to North Korea’s Lazarus Group, a name that keeps showing up whenever there’s a large-scale, high-precision breach.
Case Study: DMM Bitcoin — May 2024
A vulnerability in DMM Bitcoin’s internal infrastructure allowed hackers to extract roughly $305 million, or close to 4,500 BTC.
The attack triggered global investigations and renewed scrutiny of how exchanges handle their backend security.
Case Study: WazirX — July 2024
India’s top exchange lost nearly $234.9 million when its multi-signature wallet system was exploited.
Multiple reports, including one by Halborn, pointed to architectural flaws that gave attackers a way in.
Case Study: BtcTurk — June 2024
Hackers breached BtcTurk’s hot wallet system and drained about $55 million in digital assets.
Even with a fast response from the exchange, the stolen funds were scattered across wallets, making recovery an uphill climb.
Case Study: BingX — September 2024
A coordinated attack hit BingX’s hot wallets, resulting in a $52 million loss.
Details are still emerging, but early indicators suggest internal credentials may have been compromised.
Ponzi Schemes & Fake Investment Platforms
These scams never really left — they just rebranded.
In crypto, fake investment platforms are everywhere. Flashy UIs, daily return promises, Telegram admins pretending to offer “support.” It all looks polished — until the moment it stops.
Once the inflow of new users dries up, the platform goes silent. Withdrawals freeze. The website vanishes. And the money? Usually long gone.
Retail investors often take the worst hit here. With most of these platforms run anonymously, and no real contact point, getting your funds back is next to impossible.
Why Quick Action Matters in Crypto Recovery
When crypto disappears, hesitation works in the hacker’s favor. Attackers don’t sit on stolen funds for long. They move fast — splitting assets across wallets, running them through mixers, or cashing out before anyone starts looking. After a day or two, the trail gets harder to follow. Sometimes, it vanishes altogether.
Investigators estimate that the window for recovery shrinks drastically within the first 24 hours. After that, the odds drop sharply — and the chances of a full return go from slim to nearly zero.
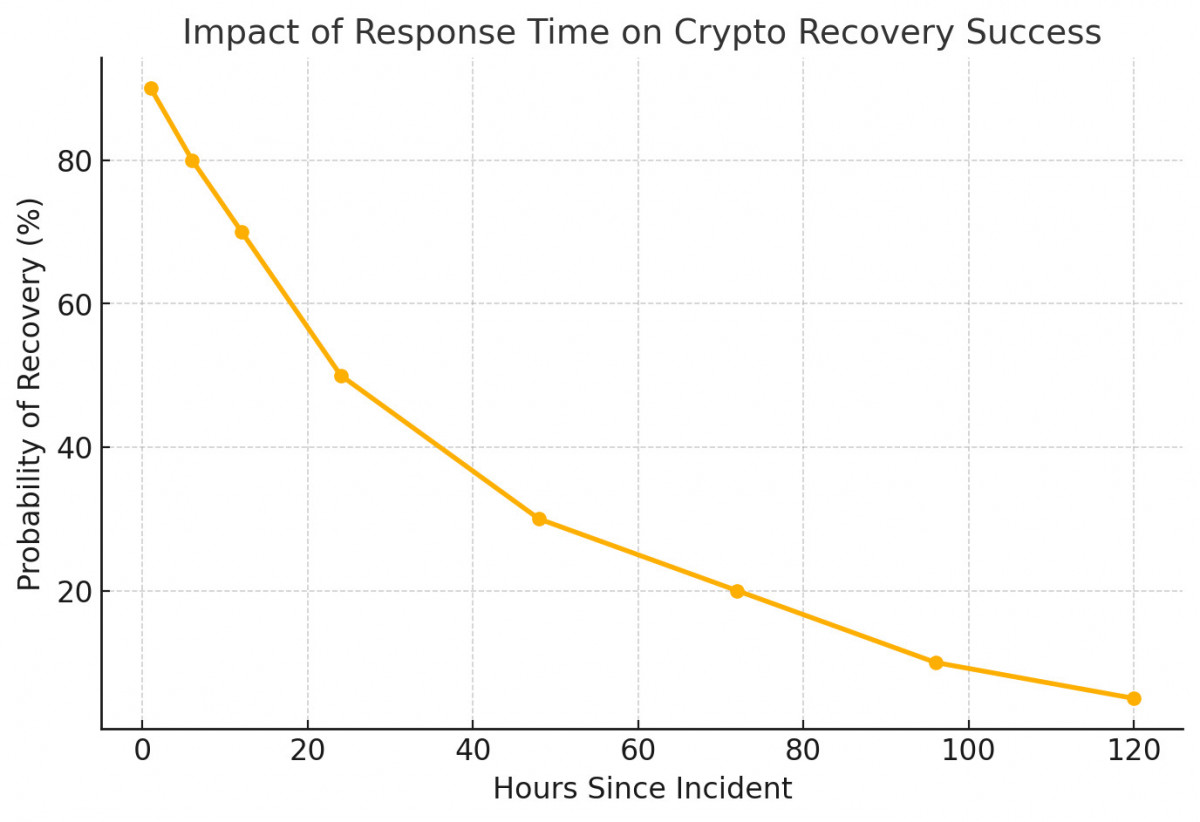
That’s why quick response matters. Not just filing a report — but getting experienced hands on the case as early as possible. Every hour counts.
How Match Systems and Other Private Companies Support Law Enforcement
Private detective firms play a crucial role in assisting law enforcement agencies in investigations related to cryptocurrency.
Main contribution:
Blockchain Transaction Analysis – using tools such as MS Engine from Match Systems, Chainalysis, TRM Labs, and Elliptic to track illegal transactions and identify criminals’ wallets. Forensic investigations are the conduct of in-depth checks of cybercrime activities.
Cooperation with law enforcement agencies – Providing support in conducting investigations, detailed reports, and expert opinions on cybercrime cases.Asset Freezing and Recovery Support – Assistance to law enforcement agencies in preparing legal requests for the freezing of funds held by Virtual Asset Service Providers (VASPs).
Crypto-related crime continues to evolve — and so do the efforts to counter it.
Successful asset recovery requires more than on-chain transparency. It depends on fast response, access to advanced forensic tools, and close coordination between public institutions and private sector specialists. While law enforcement agencies lead many investigations, they increasingly rely on support from external experts.
The takeaway is clear: the faster the response, the harder it becomes for attackers to succeed.
Disclaimer
In line with the Trust Project guidelines, please note that the information provided on this page is not intended to be and should not be interpreted as legal, tax, investment, financial, or any other form of advice. It is important to only invest what you can afford to lose and to seek independent financial advice if you have any doubts. For further information, we suggest referring to the terms and conditions as well as the help and support pages provided by the issuer or advertiser. MetaversePost is committed to accurate, unbiased reporting, but market conditions are subject to change without notice.


















































